Keeping personal information safe on the Internet may become a mission impossible when we suspect signs of a phishing email, especially when we apply bulk email marketing software and launch massive campaigns (email blaster). With the help of phishing scammers, you stay vulnerable as they force you to voluntarily give up personal or corporate data. So, you have to watch out and preserve attentiveness.
What is phishing?
Phishing is usually called a type of online scam designed to steal confidential information. Phishing email warning signs are well masqueraded by phishing scammers as large corporations or other organizations you know to trick you into voluntarily providing credit cards, domain names, images in email, private social media or other account login information, social security numbers, etc. Typically, cybercriminals contact victims via email, SMS, or social media messengers. And emails are their favorite channel.
What is a phishing email?
A phishing email is a scam that looks like an official email from a company you know or phishing email warning to employees. Such letters contain requests for confidential personal data. When you view incoming mail inattentively, there is a risk of not distinguishing between a regular email and a phishing one. Fraudsters go to great lengths to disguise phishing emails as those sent by real companies, so you should be careful when opening emails and clicking on the links they contain to avoid potential phishing attacks.
What are common indicators of a phishing attack?
Apart from sense of urgency, the person who supposedly sent you the fraudulent email may have created the letter chain to contact the company by a phishing email. The most common indicators of such type of phishing attempt usually involve tone, grammar mistakes in an email message, and the subject line.
Phishing attacks examples
What can be a real example phishing warning email? A typical one will touch upon a two-factor authentication scam. For example
A well-known two-factor authentication (2FA) has been around for a long time, and you’ve probably received emails asking you to verify your login details with a six-digit numeric code. Fraudsters also know how common two-factor authentication works, and this service, designed to protect your personal data, can be used for criminal purposes, as well.
If you receive an email asking you to sign in to verify your identity, use the criteria above to verify the authenticity of the message. Be especially wary of two-factor authentication requests for an account you haven’t used in a while.
How to recognize phishing
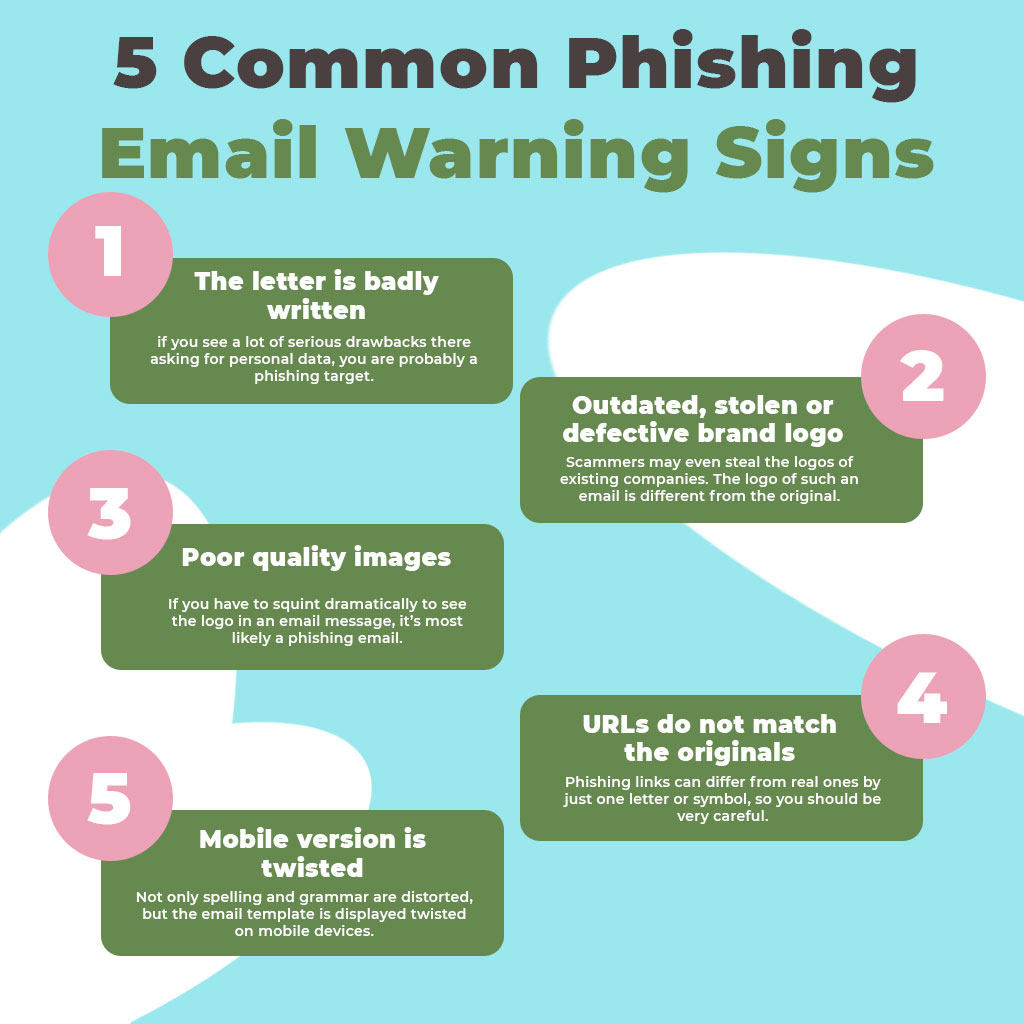
Attackers often ruin their own plans by making elementary mistakes in phishing warning email template that are easy to detect. Every time you open an email, check it for 5 basic signs.
Phishing mails contain grammar and spelling errors, and other clear signs that they were not prepared by the marketing department of large corporations. Of course, even large companies sometimes make small mistakes in emails, but if you see a lot of serious drawbacks there asking for personal data, you are probably a phishing target.
To increase the credibility of their emails, scammers may even steal the logos of existing companies which will be one of the most common signs of a phishing email signs, and nearly the most obvious. The logo of such an email is different from the original.
You should be alerted that the image is of poor quality, the aspect ratio is not respected, or the color reproduction is broken, etc. If you have to squint dramatically to see the logo in an email message, it’s most likely a phishing email.
In phishing messages, the emphasis is always on the links that the victim should follow. There are several ways to check if a link sent by email is real. In some email clients, simply hovering over the links will show its URL. You can also right-click the link, copy it, and paste the URL into any text editor. Phishing links can differ from real ones by just one letter or symbol, so you should be very careful.
Not only spelling and grammar are distorted, but the email template is displayed twisted on mobile devices. Comparing two versions will make you sure the quality is poor.
You can check the URL from the links by tapping and holding it with your fingers on your mobile devices. In the case the URL you found doesn’t match the person who supposedly sent you the email, you may have received a phishing email.
Best practices for preventing phishing attacks
To avoid becoming a victim of phishing, you should be careful when using your work email address. One of the most common phishing schemes is to send letters on behalf of the leaders of your company. They ask employees to follow a link, register in new company service, or provide personal data for reporting. In order not to fall into the bait of scammers, you need to pay attention to the format of the letter, literacy, and reliability of the text.
If you accidentally enter data on a web page associated with a suspicious email: Unplug your device and run a full malware scan to email warning about phishing. Once the scan is complete, back up all personal files and change your passwords. Even if you only gave the scammer the details of one account, you may have exposed other personal data, so it’s important to change all the passwords you use online after a suspected phishing attack.
In conclusion
Phishing mailings are designed to work out all thanks to your inattention. You should be careful with the personal data and be extremely careful if someone asks you to disclose confidential information about you, your finances, your organization or its employees, or asks for any other credentials. In order not to fall into the bait of scammers, you need to pay attention to the format of the letter, literacy, and reliability of the text. Good luck!